The scenario
Hi fellows! It’s being a while since my last post. Let’s say I am having pretty busy weeks. A lot is going on at work, don’t take me wrong, to me that’s good! The sad part is that I have less time to spend with the community.
Anyway, last Friday a friend of mine came up on Skype asking me if I was aware of a malware that changes Internet Explorer’s proxy settings. I know that there’s a bunch of malwares which does it. However, the real question was: Why his machine antivirus did not detect it?
Moreover, Microsoft Security Essentials (MSE) was installed on the machine, one of the best antivirus/antispyware on the market today, and updated with the latest detection signatures.
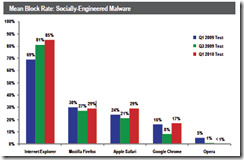
I truly recommend MSE, since it’s free of charge (you have to have a genuine Windows copy, but who doesn’t?  ), it uses the same engine as Forefront Endpoint Protection (Microsoft antivirus solution for corporate costumers), as I said before one of the best on the market, check AV-Comparatives web site.
), it uses the same engine as Forefront Endpoint Protection (Microsoft antivirus solution for corporate costumers), as I said before one of the best on the market, check AV-Comparatives web site.
Backing to the initial topic, after my friend told me that every time he rebooted his machine the malicious proxy configurations were set up again, my first though was to look for a suspicious running process.
In my humble opinion, there’s no better tool to unveil process information than Process Explorer, developed by Mark Russinovich. Next step, was download and run it on the affected computer.
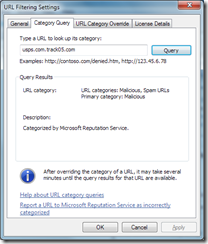
At this moment I identified a suspicious .vbs file named amsfx.vbs. This Visual Basic script file was configured to change many registry key configurations, including the browser’s proxy settings, and also was calling an executable file named dwm.exe. I know what you’re might thinking, this executable is the Desktop Window Manager for Windows Vista and Windows 7 Operating Systems, although, the OS running on the machine is Windows XP.
That said, it is clearly this executable file was malicious. However, how to confirm this info if the MSE did not detect it?
The solution
I told him that I submitted the above files to Microsoft Malware Protection Center (MMPC) for their analysis and if confirmed as malware the MSE database signature will be updated with this new threat. Some of you might think: “Why not use another antivirus solution and remove the threat?” or “I don’t think MSE is good enough”.
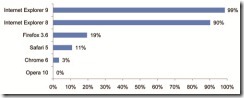
The answer to this question is that only the following antivirus suspected (did not identified it) the .exe was malicious:
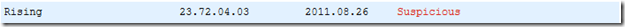
After I submitted the file, the time frame between malicious file submission and release of new detection signature was like below:
Submission status history:
Analysis Completed: Aug 29, 2011 01:46 PM UTC
Preliminary Result Available: Aug 29, 2011 09:07 AM UTC
Under Active Investigation: Aug 26, 2011 02:46 PM UTC
Received: Aug 26, 2011 12:49 PM UTC
That was fast, isn’t it? Considering it was sent on Friday and the new detection signature was available on Monday. I must say it is no surprise to me. All possible malicious file that I receive, I send to MMPC for analysis. The majority of the times the answer is like that, real fast.
I also send these samples to other antivirus providers, but the speed to respond and create a new signatures are not that fast. You must note that I don’t need a special contract or anything like it to send and get fast responses. Microsoft is really committed to provide us better security.
After that, I checked again on Virus Total web site and the only antivirus solution that really identified the malware was MSE.
At time of this writing a few more AV solutions now identifies this new malware. Check here.
If you would like to see the final report, check here.
Final message
The bottom line here is if you think your machine is infected and even if your AV solution does not detect any threats, you can search for the (possible) malicious file and send the sample to your antivirus provider to analyze and create a signature for the new threat helping every one out there!
If you are like my buddy and I, chose Microsoft Security Essentials, then you can access MMPC website or use this link to submit a suspicious file.
Regards,
Paulo Oliveira.